How security professionals stopped one botnet attack from getting much worse.
Even one of the simplest forms of cyberattack has the potential to catastrophic damage; a large DDoS attack by an army of hijacked devices is capable of knocking networks offline, leaving organisations and their customers unable to access services.
The impact of such an attack was made clear by the Mirai botnet incident late last year. The Mirai botnet used everyday internet-connected devices, such as routers and security cameras, to bring large chunks of the internet to its knees, slowing or outright bringing down popular websites and services.
But that wasn't the end of Mirai's malicious intent. A month later a million internet users in Germany were thrown offline in late November as part of a coordinated cyberattack which also impacted the UK, Ireland, Turkey, Iran, and Brazil, among others.
Internet provider Deutsche Telekom bore the brunt of much of the attack within German borders. Matthias Rosche, SVP of solution sales and consulting at Deutsche Telekom's telecom security group, described it as "the biggest attack" against the company which had a "major" impact on its customer base.
Almost five percent of its 20 million customers suffered internet outages as a result of the botnet attack, which targeted ZYxel and DLink routers, exploiting an open port. In total, 900,000 routers were affected by the attack.
The attack wasn't capable of stealing data, but it still created massive problems, resulting in 30 hours of downtime for 900,000 internet connections in homes and businesses across Germany.
"What we saw was that there were specific routers which had issues and problems. Looking at the statistics, we saw that a significant number went down immediately," Rosche said, speaking at a conference arranged by security company Check Point in Milan.
The malware contained a link designed to upload malicious software to the devices in order to connect them to the botnet, but Deutsche Telekom quickly moved to minimise the potential damage of this threat.
"We started to investigate into the attack and figured out there was a download link embedded to upload to malicious software. So the first thing we did was block that to make sure that even if the infection is successful, nothing can be uploaded from that specific link," said Rosche.
The company's security team set up a war room to coordinate activities and block the key target open port across the network, in order to ensure no attack could target it anymore, he explained.
In addition to this, an agreement between Deutsche Telekom and the router vendors meant as soon as the telecoms firm knew how to close the vulnerability, they contacted the vendors and provided them with the information required to update devices and protect them against the botnet.
"Within 12 hours we had a new software version available for our routers," said Rosche, adding that users were informed they had to turn routers on and off again and to protect themselves from the attack.
"This was a simple patching process and we were happy this was our worst-case scenario," he said of the incident.
If the attack had been fully successful, the results would've been dire and a danger to the internet.
"It's a simple calculation. We'd have had a new botnet of 1.8 terabits per second, which is big enough to carry out a DDoS attack against any state in the world. This would've been the most powerful weapon on the internet, it would have been incredible," said Rosche.
"We apologised to our customers and the question we had to ask ourselves was, 'Can we guarantee that this won't happen again in the future?' The answer is 'probably not'. But we'll be prepared," he said.
From:http://www.zdnet.com/article/botnets-the-race-to-stop-the-most-powerful-weapon-on-the-internet/
About OsMonitor:
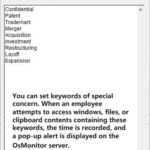
The mission of OsMonitor is to create a Windows computer system tailored for work purposes, effectively regulating employee computer behavior. It enables employers to understand what employees are doing each day, monitoring every action, including screen activity and internet usage. Additionally, it restricts employees from engaging in specific activities such as online shopping, gaming, and the use of USB drives.
OsMonitor, designed purely as software, is remarkably user-friendly and requires no additional hardware modifications. A single management machine can oversee all employee computers. As a leading brand in employee computer monitoring software with over a decade of successful operation, OsMonitor has rapidly captured the global market with its minimal file size and excellent cost-effectiveness compared to similar software. At this moment, thousands of business computers worldwide are running OsMonitor daily.